Managed IT & Cybersecurity Services
From augmenting your internal IT team to providing end-to-end IT support, our Managed IT & Cybersecurity Services offer flexible solutions tailored to your specific needs.
From augmenting your internal IT team to providing end-to-end IT support, our Managed IT & Cybersecurity Services offer flexible solutions tailored to your specific needs.
Managed IT & Cybersecurity Services for On-Premises, Cloud, and Hybrid environments.
Solutions custom-fit to your operational needs and business growth.
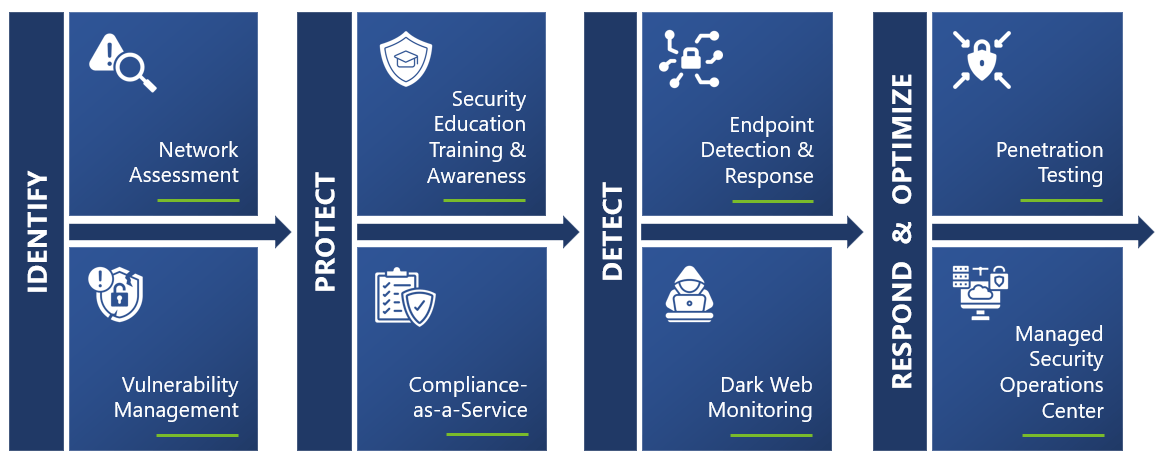
Our approach to Managed IT and Cybersecurity Services goes beyond break-fix technical support to a single-source IT partner—so you can focus on the things that matter for your business.
Our methodology encompasses Onboarding, End-User Support, Infrastructure Management, Cybersecurity Services, and Strategy to not only maintain what you have today but help your business forge a path to greater success through technology.

With our services, every member of your team can enjoy unlimited support for any issues or questions related to your managed devices. Our expert technicians are available to assist you promptly, ensuring minimal disruption to your workflow.
Our team closely monitors your managed workstations around the clock, utilizing advanced monitoring tools and techniques. This proactive approach allows us to detect and resolve problems swiftly, ensuring your systems are always up and running.

Artificial intelligence is no longer a future consideration—it’s reshaping business operations today. For small and medium-sized businesses, AI represents both […]

Running a small or mid-sized business (SMB) means wearing many hats, but IT doesn’t have to be one of them. […]

Transforming Quality Management in a Regulated Manufacturing Environment How a highly regulated manufacturer streamlined compliance, improved audit readiness, and scaled […]

Empowering Growth with a Smarter ERP How Abel Solutions redefined McBride’s Traverse ERP to meet modern demands Heritage Meets Innovation […]

Many businesses don’t realize it, but employees, vendors and even software applications often have more access than they need. This […]
Most businesses today depend on third-party partners. These partners may provide products, services, or even expertise that help keep your […]
Despite believing they were immune, a small law firm in Maryland fell victim to a ransomware attack, exposing sensitive and […]

Imagine a workplace where every employee is vigilant against cyber threats, a place where security isn’t just a protocol but […]

Scaling Up With Modernized Email and Streamlined Licensing Costs Overview A property management company with about 50 users and 20 […]




Our per-device Managed Services model combines IT support and cybersecurity services, ensuring comprehensive coverage across your entire digital operations, from desktop to mobile devices, on-prem servers to cloud, and the underlying infrastructure.
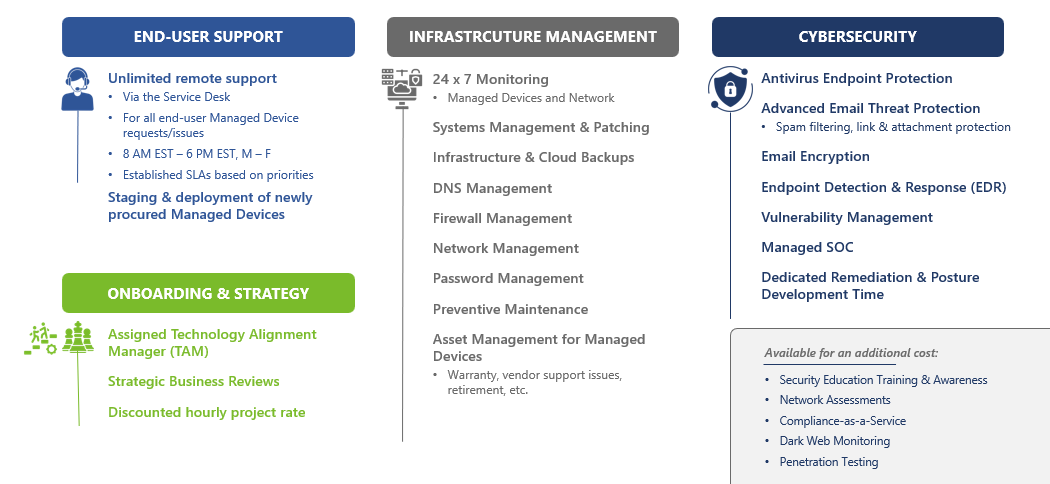
To ensure ongoing optimization and improvement, we conduct regular Strategic Business Reviews. These assessments help us identify opportunities for enhancing your IT environment, addressing pain points, and streamlining operations, ensuring that your technology continuously evolves alongside your business.